Securinets CTF 2019 — Lost Flag (Exploiting Bazaar VCS)
Discover a hidden Bazaar VCS repository on a web server, clone it, and revert to a previous revision to recover a deleted flag file.
A web challenge where the flag was deleted but recoverable through version control history.
Challenge Details
Category: Forensics/Web | Points: 994 | Solves: 19
Help me get back my flag!
Reconnaissance
Login with admin/admin — we’re in, but the flag is gone. Standard directory enumeration with dirsearch:
python3 dirsearch.py -u https://web8.ctfsecurinets.com/ -e php,html,txtDiscovery: /.bzr/README — a Bazaar version control repository is exposed!
What is Bazaar?
Bazaar (bzr) is a distributed version control system similar to git. Exposing .bzr/ is equivalent to exposing .git/ — it leaks the entire commit history.
Extracting the Repository
bzr branch -Ossl.cert_reqs=none https://web8.ctfsecurinets.com/Note: use bzr branch, not bzr clone.
Examining History
bzr log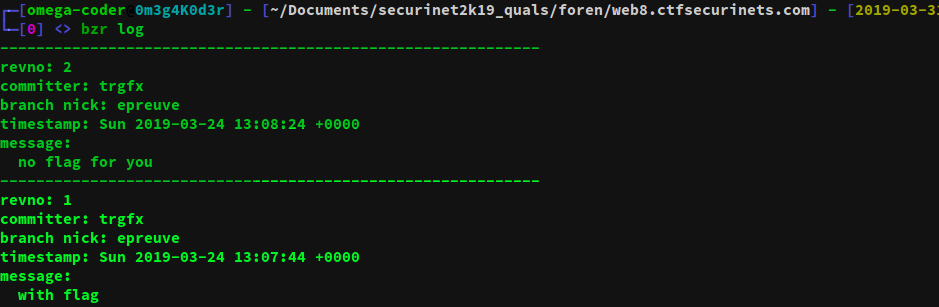
Output shows two revisions:
- Revision 2: “flag deleted”
- Revision 1: Original commit with the flag
Recovering the Flag
bzr revert -r 1This restores all files to revision 1, bringing back flag.php.
Flag: Securinets{BzzzzzzzzZzzzzzzzzzZrR_roCk$}
Key Takeaways
- Never expose
.git/,.svn/,.bzr/, or.hg/directories to the web — they leak full source history - Use your web server config to block access to version control metadata directories:
# nginx
location ~ /\.(git|svn|bzr|hg)/ {
deny all;
return 404;
}# Apache
RedirectMatch 404 /\.(git|svn|bzr|hg)- Tools like GitDumper and dvcs-ripper automate VCS extraction — pentesters should always check for these